Synopsys tRoot™ Hardware Secure Modules (HSMs) with Root of Trust enable connected devices to securely and uniquely identify and authenticate themselves to create secure channels for remote device management and service deployment. The pre-built tRoot Vx HSM family offers a defined security boundary for a complete, drop-in security solution, while the flexible tRoot Fx HSM family includes fully programmable and highly configurable solutions that enable designers to tune the HSM to their exact requirements. tRoot HSMs are designed to easily integrate into SoCs and provide robust hardware-enforced protection while maintaining a high level of performance through cryptographic acceleration. They offer designers options to create solutions with the most efficient combination of power, size and performance. tRoot HSMs provide a Trusted Execution Environment (TEE) to protect sensitive information and processing, and implement security-critical functions such as secure boot, storage, debug, anti-tampering and key management required throughout the device life cycle.
The Synopsys tRoot Vx HSM provide SoCs with a unique identity that cannot be tampered with, and extend the trust of that identity to other internal and external entities in the SoC.
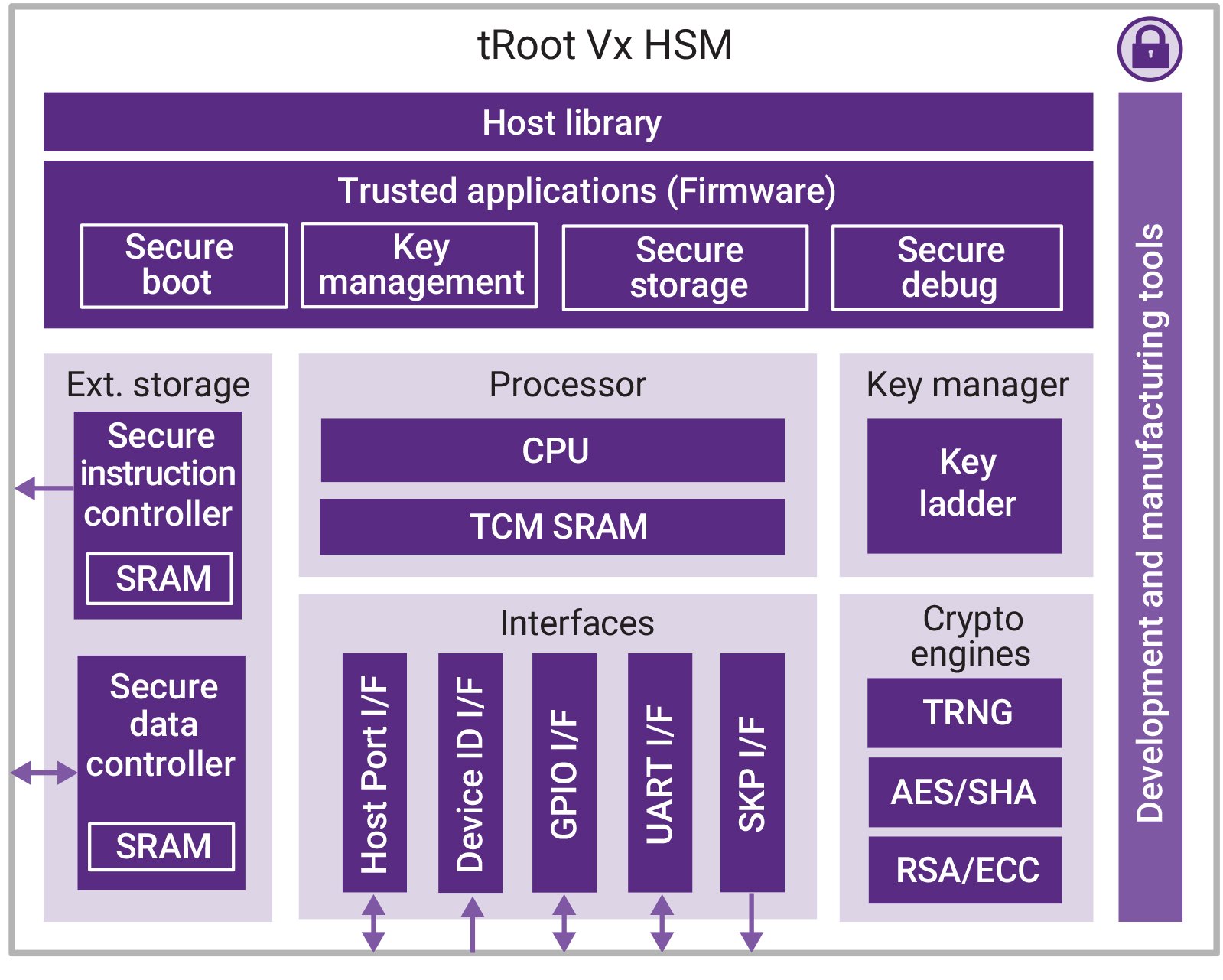
The Synopsys tRoot Vx HSMs provide security functions in a trusted environment as a companion to a host processor. The secure instruction and data controllers provide protected access and runtime tamper detection in external memories for code and data privacy protection without the added cost of additional dedicated secure memory. In addition, they reduce system complexity and cost by allowing tRoot’s firmware to reside in any non-secure memory space. Its unique architecture can effectively adjust to future security requirements and standards.
The complete, standalone products provide a secure hardware enclave with firmware components and tools, allowing designers to quickly integrate a security solution without requiring expertise to write security software. With the Synopsys Vx tRoot HSMs, designers can easily create, store and manage secrets that are critical in industrial control, cellular communications and IoT hubs.
Highlights & Key Features
- Complete hardware secure modules with Root of Trust give SoCs a unique, tamper-proof identity
- Enable secure services deployment
- Provide a Trusted Execution Environment to create, provision, store and manage keys
- Crypto APIs based on PKCS #11
Find Your IP
Search for IP
Quickly identify and access the right IP solutions for your project needs.
Foundation IP Selector
Find embedded memory and logic IP for your SoC design.
Non-Volatile Memory IP Selector
Find silicon-proven NVM IP for your SoC design needs.






