Subscribe
The Internet of Things is all around us. But it doesn’t stop there—now it’s inside us too. As the era of “connected everything” explodes, so does the use of network-connected medical devices. These interconnected devices, ranging from hospital imaging equipment to implantable pacemakers to infusion pumps, help healthcare providers and patients in a variety of tasks—monitoring vitals, regulating dosages, improving diagnostics, and more. But the convenience of this functionality comes with a trade-off: vulnerability. If attackers gain access to a connected medical device, the potential consequences include severe injury and even death. Consider this:
- U.S. hospitals have an average of 10–15 connected medical devices per bed.
- More than 100,000 devices and systems are publicly exposed at healthcare organizations worldwide.
- A 2011 review suggested that at least 6.7 million people in the United States receive medical device implants every year.
- An analysis of 50 hospitals found these security issues in their connected medical devices:
- User practice issues (41%): The device can download unapproved applications or visit risky websites
- Outdated operating systems and software (33%)
- Lateral movement (12%): An attacker gaining access to the device can access other devices and systems on the network
- Unprotected communications and weak passwords (11%)
- Network segregation (3%): The network the device is on provides too much access for the device’s needs
How secure are your network-connected medical devices?
Given these statistics, it isn’t surprising that among medical device manufacturers, two-thirds believe an attack on a medical device they built is likely within the next year. But only 17% have taken significant steps to prevent an attack. Making matters worse, less than half of manufacturers—and only 22% of healthcare delivery organizations—have a device incident response plan in place.
Thankfully, reports of device hacks are still rare, and there have been no deaths. It seems that so far, the benefits outweigh the risks. And the FDA’s adoption of UL 2900-2-1 as a premarket certification standard is a step in the right direction. But the number of vulnerabilities identified—and recalls and updates issued—is increasing steadily. Check out the timeline below to learn more about the history of security vulnerabilities in medical devices.
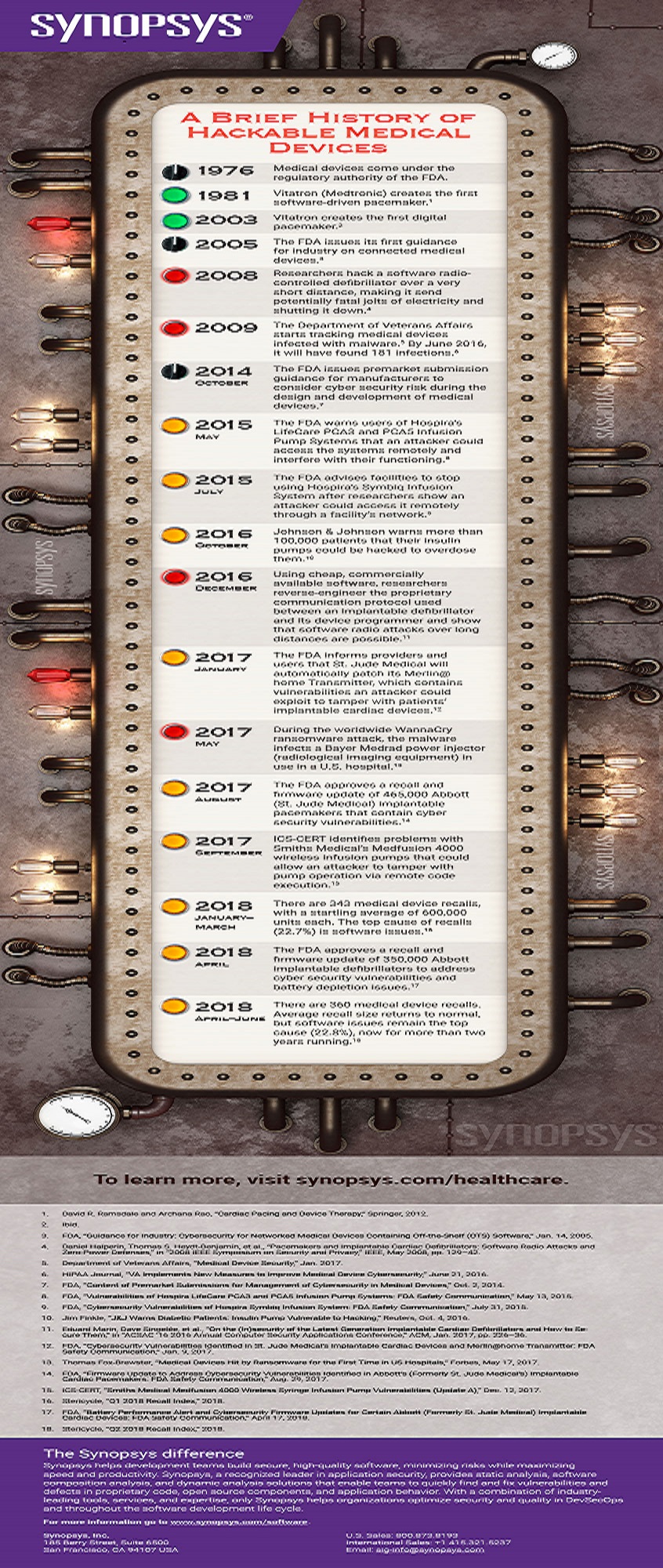
A Brief History of Hackable Medical Devices
1976 Medical devices come under the regulatory authority of the FDA.
1981 Vitatron (Medtronic) creates the first software-driven pacemaker.
2003 Vitatron creates the first digital pacemaker.
2005 The FDA issues its first guidance for industry on connected medical devices.
2008 Researchers hack a software radio-controlled defibrillator over a very short distance, making it send potentially fatal jolts of electricity and shutting it down.
2009 The Department of Veterans Affairs starts tracking medical devices infected with malware. By June 2016, it will have found 181 infections.
Oct. 2014 The FDA issues premarket submission guidance for manufacturers to consider cyber security risk during the design and development of medical devices.
May 2015 The FDA warns users of Hospira’s LifeCare PCA3 and PCA5 Infusion Pump Systems that an attacker could access the systems remotely and interfere with their functioning.
July 2015 The FDA advises facilities to stop using Hospira’s Symbiq Infusion System after researchers show an attacker could access it remotely through a facility’s network.
Oct. 2016 Johnson & Johnson warns more than 100,000 patients that their insulin pumps could be hacked to overdose them.
Dec. 2016 Using cheap, commercially available software, researchers reverse-engineer the proprietary communication protocol used between an implantable defibrillator and its device programmer and show that software radio attacks over long distances are possible.
Jan. 2017 The FDA informs providers and users that St. Jude Medical will automatically patch its Merlin@home Transmitter, which contains vulnerabilities an attacker could exploit to tamper with patients’ implantable cardiac devices.
May 2017 During the worldwide WannaCry ransomware attack, the malware infects a Bayer Medrad power injector (radiological imaging equipment) in use in a U.S. hospital.
Aug. 2017 The FDA approves a recall and firmware update of 465,000 Abbott (St. Jude Medical) implantable pacemakers that contain cyber security vulnerabilities.
Sept. 2017 ICS-CERT identifies problems with Smiths Medical’s Medfusion 4000 wireless infusion pumps that could allow an attacker to tamper with pump operation via remote code execution.
Jan.–March 2018 There are 343 medical device recalls, with a startling average of 600,000 units each. The top cause of recalls (22.7%) is software issues.
April 2018 The FDA approves a recall and firmware update of 350,000 Abbott implantable defibrillators to address cyber security vulnerabilities and battery depletion issues.
April–June 2018 There are 360 medical device recalls. Average recall size returns to normal, but software issues remain the top cause (22.8%), now for more than two years running.





